Contact us
For more information please contact one of our Solution or Service experts today.
Information provided within this form will be handled in accordance with our privacy statement.

Here’s a moment most IT teams would recognise. Something breaks, or…

Back in the age of typewriters, there was a simple standard everyone understood: the machine either…

This blog explores what the upcoming end‑of‑life milestones mean for organisations running on‑prem…

In March, I had the opportunity to take part in ‘The Great Generational Debate’ for Women in…
April 16, 2026; Brisbane, Australia: Leading Australian technology services and solutions provider,…

In March 2026, I attended Cisco Partner Technical Exchange (PTX) for the first time, not quite knowing…

As networks become more distributed, security must move closer to the workload. Discover how Cisco Smart…

April 10, 2026; Brisbane, Australia: Leading Australian technology services and solutions provider,…

In partnership with Microsoft, Data#3 has developed a K-12 Security Blueprint and whitepaper for school…
March 30, 2026; Brisbane, Australia: Leading Australian technology services and solutions provider,…
Network refresh decisions are usually driven by a specific priority, such as strengthening segmentation,…
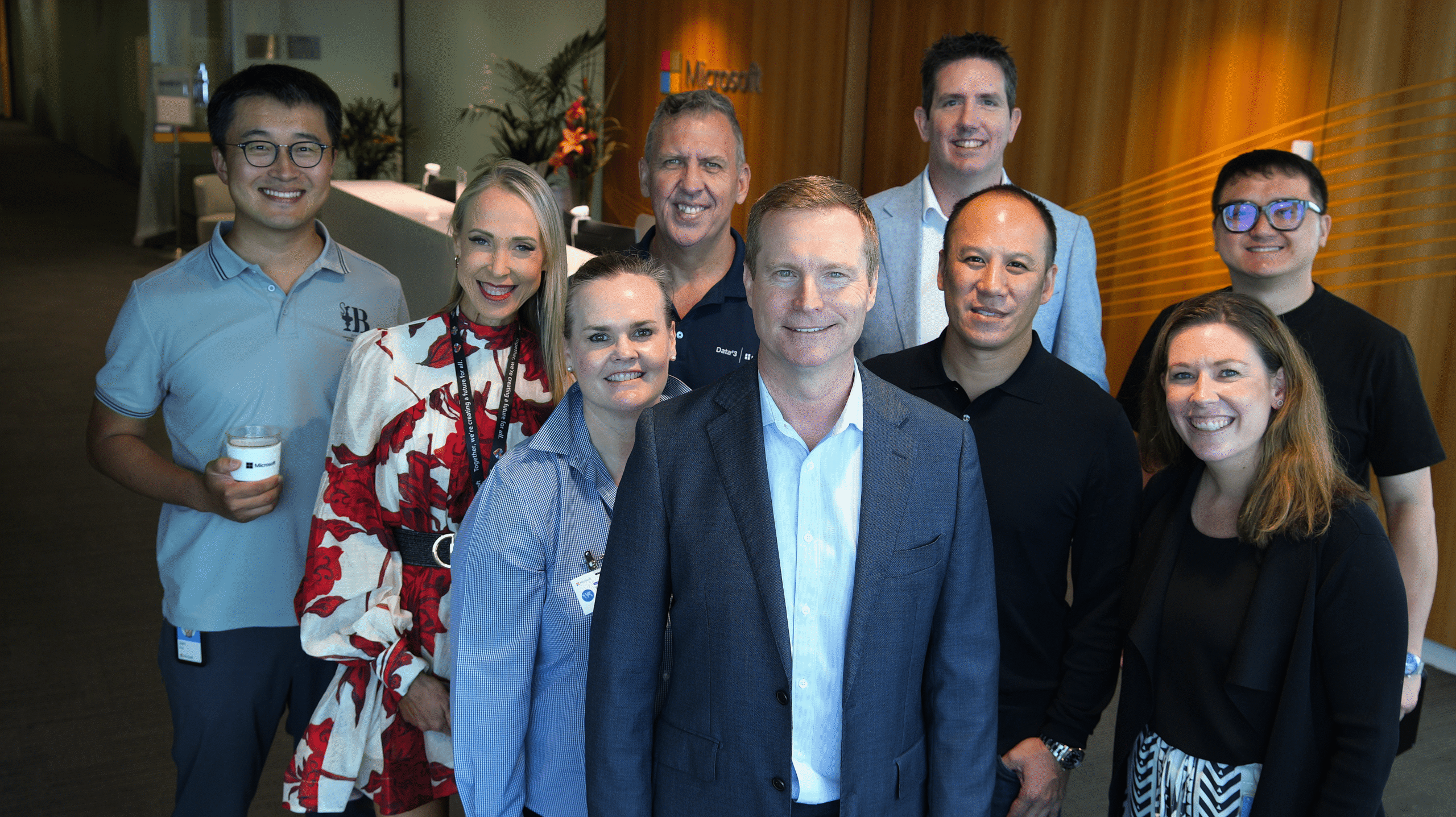
Last month, #TeamD3 ran our first in-person hackathon, BotQuest, in partnership with Microsoft….

For more information please contact one of our Solution or Service experts today.

For more information please contact one of our Solution or Service experts today.
Information provided within this form will be handled in accordance with our privacy statement.